Struggling to stay ahead in the ever-changing world of cyber threats? Organizations today must handle massive data volumes and respond to incidents swiftly. Managing cybersecurity has become increasingly challenging.
Enter Microsoft Security Copilot—a cutting-edge, AI-powered security solution. Designed to enhance your team’s ability to protect your network, it delivers customized insights and works seamlessly with other Microsoft security tools. With natural language integration, it offers clear, actionable guidance to simplify your defense strategy.
In this article, we’ll dive into what Microsoft Security Copilot is, its key advantages, and how it can strengthen your cybersecurity efforts.
What Is Microsoft Security Copilot?
Microsoft Security Copilot is an advanced cybersecurity tool powered by AI and machine learning. It’s designed to make threat detection and response faster and more effective, improving the overall efficiency of cybersecurity operations.
Key benefits of Microsoft Security Copilot include:
- Responding to cyber threats
- Analyzing signals
- Assessing risk exposure at incredible speed
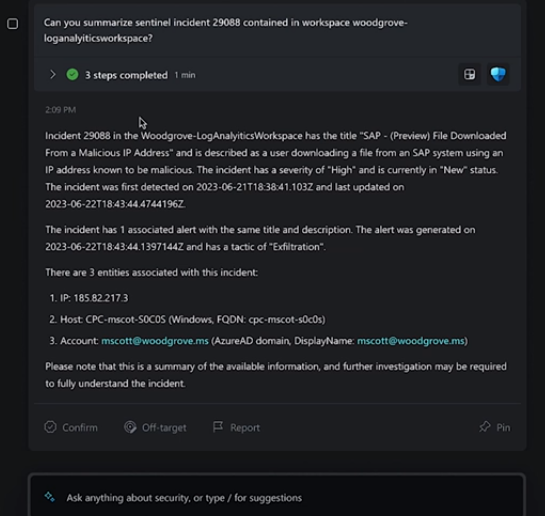
It integrates seamlessly with other Microsoft security tools and uses natural language, allowing you to ask questions directly and receive tailored guidance and insights.
Microsoft Security Copilot supports various end-to-end tasks, including:
- Incident response
- Threat hunting
- Intelligence gathering
- Security posture management
- Summarizing investigations for executives
This tool empowers security teams to navigate the complex threat landscape with ease and confidence.
How Does Microsoft Security Copilot Work?
Microsoft Security Copilot can be accessed as a standalone tool or through embedded features within other Microsoft security products.It integrates with several tools, including:
- Microsoft Sentinel
- Microsoft Defender XDR
- Microsoft Intune
- Microsoft Defender Threat Intelligence
- Microsoft Entra
- Microsoft Purview
- Microsoft Defender External Attack Surface Management
- Microsoft Defender for Cloud
With Security Copilot, you can use natural language prompts, making it easy to request information or guidance on different security topics.
For example, you can ask:
- “What are the best practices for securing Azure workloads?”
- “How does CVE-2024-23905 impact my organization?”
- “Can you generate a report on the latest attack campaign?”
- “How do I handle an incident involving TrickBot malware?”
This user-friendly approach helps you quickly get the insights and support you need for effective cybersecurity.
Should You Use Microsoft Security Copilot?
Pros:
- Advanced Threat Detection
Microsoft Security Copilot uses advanced algorithms to detect and analyze threats that might be missed by traditional security measures. It adapts in real-time to new threats, strengthening an organization’s overall security posture. - Operational Efficiency
Copilot automates threat analysis, allowing security teams to focus on strategic decisions. This reduces time spent on manual data analysis and streamlines workflows, leading to faster responses to potential threats. - Integration with Microsoft Products
Security Copilot integrates smoothly with various Microsoft products, creating a unified cybersecurity ecosystem. The combination of these tools boosts both threat visibility and response capabilities. - Continuous Learning
Powered by AI and machine learning, Copilot constantly learns from new data, improving its ability to identify and address emerging threats. This adaptive learning ensures that the tool stays effective in an ever-evolving threat landscape. - Reduced False Positives
Thanks to its advanced algorithms, Copilot enhances threat detection accuracy, minimizing false positives. This allows security teams to focus on actual threats, making their responses more focused and efficient.
Considerations:
-
- Integration Challenges
While Microsoft Security Copilot integrates smoothly with Microsoft and other security tools, organizations using a wide variety of cybersecurity solutions might face challenges with compatibility. It’s important to assess how well Copilot will fit into your current cybersecurity setup. - Resource Requirements
The advanced AI and machine learning features of Copilot may require additional resources. Companies should evaluate whether their existing infrastructure can support the tool’s resource demands. - Training and Familiarization
To fully take advantage of Copilot’s capabilities, your security team needs proper training and a good understanding of the tool’s functions. Ensuring that your team is well-prepared will help you make the most of this cybersecurity solution.
Bottom Line
Microsoft Security Copilot is a major advancement in AI-powered cybersecurity. It offers real-time threat detection, improved operational efficiency, and strong integration capabilities, making it an excellent choice for businesses looking to enhance their digital defenses.
When deciding whether to adopt Microsoft Security Copilot, it’s important to consider your unique business needs. Think about factors like your current cybersecurity infrastructure, available resources, and the commitment to ongoing training for your team.
We are your Chicago IT Support Specialist. If you need Expert Microsoft Product Support, contact us at (630) 953-3100 or by email at tg@tomorrowssolutions.com.
Microsoft offers a wide range of interconnected business tools, and Security Copilot is one of the latest additions to help secure your digital environment. If you need assistance in using these tools for your business, we’re here to help. As experienced Microsoft service providers, our team can guide you in maximizing the potential of these tools.
Contact us today at 630-202-8631 or at tg@tomorrowssolutions.com to schedule a consultation.
