Network Security Insights
Top 6 Smart Office Trends to Adopt for an Improved Workflow
The modern office is evolving rapidly, moving away from dull cubicles and repetitive tasks. Today’s smart offices are dynamic centers of creativity and collaboration, built to enhance employee performance and streamline workflows. This transformation is powered by...
Windows 10: The Final Countdown – It’s Time to Upgrade Your PC
Windows 10 has been a reliable companion, but its era is coming to an end. Microsoft plans to end support for Windows 10 on October 14, 2025. As it phases out, this means no more security updates, patches, or official support. The time has come to make the switch to...
8 Tips for Safeguarding Your Gadgets While Traveling
In today’s world, travelling with technology is essential whether for work, staying connected, or simply passing the time. Yet, with the convenience of our devices comes the risk of theft, damage, or loss while on the move. To help Protect Your Gadgets during your...
Unmasking the True Price of IT Downtime
It's a bustling Monday morning, and you step into your office, energized to seize the week. But something feels off. Computers refuse to boot up. Phones are eerily quiet. The internet? Completely dead. Your business has come to a screeching halt crippled by an...
Streamlining Success: A Guide to Task Automation for Small Enterprises
Running a small business can feel chaotic with so many tasks to manage and deadlines to meet. But what if you could save some of that precious time? That's where task automation comes in. It’s a powerful tool that helps simplify your workflow and increase efficiency....
Phishing 2.0: How AI is Amplifying the Danger and What You Can Do
Phishing has always been a threat, but with the rise of AI, it’s become even more dangerous. Phishing 2.0 is here—smarter, more convincing, and harder to spot. Recognizing this new danger is essential. A recent study showed a 60% rise in AI-powered phishing attacks....
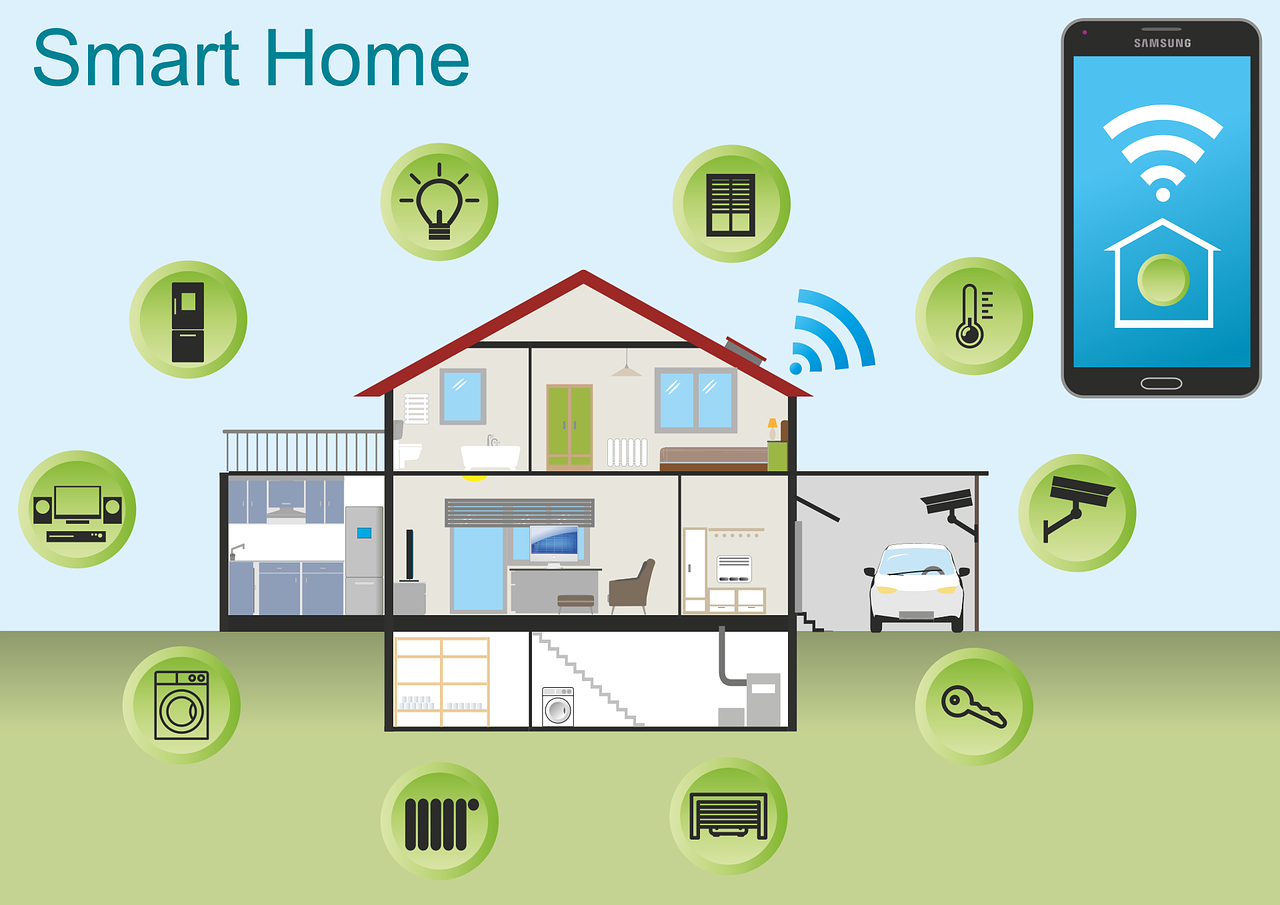
Unified Smart Homes: How Matter is Setting a New Standard
Is your Unified Smart Homes turning chaotic? Are your smart office devices not syncing? You're not alone. Many people are facing compatibility issues with their smart devices, leading to the hassle of using multiple apps and dealing with complicated setups. Smart home...
Digital Defense: Essential Security Practices for Remote Workers
The shift to remote work has transformed how we approach the workplace. Traditional office routines and commutes are now a thing of the past. However, this new flexibility also brings fresh challenges—cybersecurity risks. Digital defense in remote work setups can...
Tech-Savvy Workspaces: How Technology Drives Office Productivity
The days of cluttered desks and filing cabinets are behind us. Today’s office is a place of innovation, with technology leading the way. The right tech tools can greatly improve your team's productivity by simplifying workflows and enhancing collaboration. Is your...
AI Data Breaches are Rising! Here’s How to Protect Your Company
Artificial intelligence (AI) is quickly changing industries by providing businesses with new solutions and automation tools. However, this growth also brings concerns about AI data breaches. As AI becomes more embedded in our systems, the risks of data breaches grow....
7 Important Considerations Before You Buy Smart Home Tech
Smart homes may feel like they belong in a sci-fi film. With voice-controlled lights, self-adjusting thermostats, and robot vacuums cleaning your floors, they seem too good to be true. It’s exciting, but before you grab the latest device, there are important factors...
What Is Conversational Ai? Examples And Platforms
Several tools claim to detect ChatGPT-generated text, but in our checks, they’re inconsistent at finest. ChatGPT is AI-powered and utilizes LLM know-how to generate text after a prompt. After being delayed in December, OpenAI plans to launch its GPT Store someday...
Why Continuous Monitoring is a Cybersecurity Must
Imagine you're heading out for a vacation. You live in a questionable neighborhood and trust your locks to keep your home safe, but you don't check them every day. Could they be fully secure? A small crack or unnoticed flaw might have appeared. It's a potential...
A Simple Guide to the Updated NIST 2.0 Cybersecurity Framework
Keeping up with security threats is a challenge for businesses of all sizes. Between February and March of 2024, global security incidents rose by 69.8%. To protect your organization, it's crucial to adopt a structured approach to cybersecurity. The National Institute...
Hot off the Digital Presses… Learn About Microsoft Copilot for Finance
Microsoft Copilot has been at the forefront of business AI, already enhancing tools like Word, Excel, Edge, Windows, and more. Now, this generative AI-powered app is expanding into various business functions, with finance being the latest. Microsoft Copilot for...
iPhone Running Slow? Speed It up with One of These Tips
iPhones are incredible devices, no doubt about it. However, even the fastest and most stylish iPhone can start to slow down. Apps might take ages to load, and scrolling can feel laggy. Before you know it, what used to be quick and easy becomes a frustrating...
Is Your Business Losing Money Because Employees Can’t Use Tech?
New technology can be exciting! It offers the potential for better efficiency, happier teams, and a stronger position in the market. It's also essential to remain competitive in today’s tech-focused business world. However, if you overlook two key aspects—employee...
10 Easy Steps to Building a Culture of Cyber Awareness
Cyberattacks are a major risk in today’s digital age. Phishing emails, malware, and data breaches can severely harm businesses and personal lives. A lot of these threats enter a company’s network because of employee mistakes. Often, it’s a lack of cyber awareness...
What Were the Coolest Consumer Products Showcased at CES 2024?
This year’s Consumer Electronics Show (CES) was truly thrilling, giving us an incredible preview of what the future of technology holds. CES 2024 unveiled an impressive lineup of groundbreaking gadgets, from transparent TVs to robotic pet companions. These innovations...
Smart Tips for Building a Smart Home on a Budget
Picture this: the lights flicker on as you walk through the door, your coffee brews automatically before your alarm goes off, and a simple voice command adjusts the thermostat to your ideal temperature. This isn’t just futuristic fiction anymore—it’s the reality of...
Guide to Improving Your Company’s Data Management
Data is the foundation of today's businesses. It drives decision-making, uncovers insights, and powers your company's growth. However, in an era dominated by information, managing data can quickly become a complex task. With disorganized spreadsheets, fragmented...
How Synthetic Intelligence Is Reshaping The Monetary Companies Industry Greece
Transform Your Business With AI Software Development Solutions https://www.globalcloudteam.com/ — be successful, be the first! Customer Service And Personalization AI, as it ought to be broadly understood, has already been impacting financial markets for a few years....
Don’t Risk It! Why You Shouldn’t Skip Vulnerability Assessments
Cyber threats are a constant challenge for business owners, as hackers are always finding new ways to take advantage of system vulnerabilities. A proactive stance on cybersecurity is crucial for businesses of all sizes, and one key aspect of this strategy is...
7 Common Pitfalls When Adopting Zero Trust Security
Zero Trust security is revolutionizing the cybersecurity landscape by shifting away from traditional perimeter-based models. This approach ensures that every connection attempt is constantly verified before granting access to resources, reinforcing security at every...
4 Ways Small Businesses Can Leverage Copilot for Microsoft 365
What are some key factors that can drive small businesses forward? Efficiency, productivity, and innovation play a crucial role. Microsoft has made one of its most transformative tools available to small and medium-sized businesses, offering a real opportunity for...
Introducing the New Microsoft Planner (Everything You Need to Know)
Calendars, task lists, and project planning are essential for business operations. Many people rely on Microsoft tools like Planner, To Do, and Project for the web to manage these tasks. These tools keep processes organized and ensure accountability. However, since...
How to Properly Deploy IoT on a Business Network
The Internet of Things (IoT) is no longer just a futuristic idea—it's actively transforming industries and how businesses function. IoT refers to smart, internet-connected devices. For example, smart sensors can track production lines, and connected thermostats can...
Here Are the Top CyberSecurity Threats and Trends to Prepare for in 2024
As cybersecurity threats continue to evolve rapidly, staying proactive is essential. News reports highlight the rise in cybersecurity threats and trends each week, making it critical to protect sensitive data. The sophistication and frequency of data security risks...
Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Have you been hearing more about email authentication lately? There’s a good reason for that: phishing is a major security threat. It continues to be the leading cause of data breaches and security issues, and this has been ongoing for years. Google and Yahoo, two of...
Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever watched a video of your favorite celebrity saying something shocking, only to later find out it was fake? Or maybe you've gotten an urgent email that seemed to be from your boss, but something felt wrong? This is the world of deepfakes. It’s a...
Banking operations for a customer-centric world
Use decision engines to efficiently identify, review, and validate files, simplifying your banking and finance processes. ATMs provide convenience for customers by allowing quick self-service actions like deposits, cash withdrawals, bill payments, and transfers. From...
10 Most Common Smart Home Issues (and How to Fix Them)
When you were a kid, the idea of a “smart home” probably felt like something out of a futuristic movie, like Back to the Future II or The Jetsons. While we may not have flying cars yet, we do have video calls, smart fridges, and voice-activated lights. However, even...
What Is Microsoft Security Copilot? Should You Use It?
Struggling to stay ahead in the ever-changing world of cyber threats? Organizations today must handle massive data volumes and respond to incidents swiftly. Managing cybersecurity has become increasingly challenging. Enter Microsoft Security Copilot—a cutting-edge,...
Smart Tactics to Reduce Cloud Waste at Your Business
Here’s a refined version: Cloud computing has transformed the way businesses function, offering scalability, flexibility, and cost-efficiency. However, it also introduces a hidden challenge: cloud waste. Cloud waste refers to the unnecessary expenditure of resources...
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
In today's world, digital connectivity shapes every aspect of our lives. The significance of cybersecurity cannot be emphasized enough. As technology progresses, so do the increasingly sophisticated threats in the digital landscape. Many times, we unknowingly make...
Be Careful When Scanning QR Codes – There’s a New Scam Going Around!
QR codes are now ubiquitous in everyday life. You can spot them on restaurant menus, advertisements, and posters, seamlessly bridging the gap between offline and online interactions. They’re incredibly simple to use just scan with your smartphone camera, and you’re...
9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming increasingly popular and convenient, but they also present significant security risks. Hackers can exploit these devices to gain access to personal information, monitor your activities, or cause damage to your home. The dangers...
5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity Predictions for 2024 highlight the rapidly changing landscape, with new threats, technologies, and opportunities emerging each year. As we move into 2024, businesses must stay informed about existing and upcoming cyber risks. It's essential for...
Workspaces, a VPN & More – Learn the Newest Microsoft Edge Features
Microsoft Edge is continuously reshaping the browsing experience, thanks to Microsoft’s relentless innovation. The latest updates introduce a range of new features that aim to boost productivity, security, and overall browsing satisfaction. While Chrome has long held...
These 7 AI Trends Are Sweeping the Cybersecurity Realm
Relentless progress in digital technology has revolutionized recent years, with AI trends highlighting the fusion of AI and cybersecurity as a critical cornerstone for protecting sensitive information and digital assets. AI-driven innovations are rapidly transforming...
Online Security: Addressing the Dangers of Browser Extensions
Browser extensions have become as ubiquitous as mobile apps, with users often downloading many but using only a few. With over 176,000 extensions available on Google Chrome alone, these tools offer enhanced functionality and customization for browsing. However, while...
How Small Businesses Are Unlocking Growth With Generative AI
Staying ahead in business often requires adopting the latest technologies, which can open up new possibilities for growth, especially for small businesses. SMBs are constantly seeking cost-effective ways to gain a competitive edge. One game-changing innovation is...
Examples of How a Data Breach Can Cost Your Business for Years
In today’s digital world, data is the foundation of business success. It drives operations, informs decisions, and shapes customer experiences. However, lurking beneath this data-driven landscape is the ever-present threat of data breaches. The consequences of a data...
Are Your Smart Home Devices Spying On You? (Experts Say, Yes!)
Smart home devices have become a staple of modern living, offering unmatched convenience, efficiency, and seamless connectivity. However, a recent study has raised alarms about the potential privacy risks associated with these gadgets, suggesting they might be...
Why Network Security is Important?
Have you ever considered the significance of network security? It plays a vital role in safeguarding the IT infrastructure of any organization. As businesses increasingly shift their operations online and interconnectedness becomes the norm, the importance of network...
Onsite And Remote Services To These Cities
Contact Tomorrow’s Internet Solutions Today
Thank You for visiting our site. We are available for remote and onsite service. On most days, we are available by phone starting at 6:30 AM for remote support or a free consultation.
With over sixty years of in-house IT experience, our team can install, maintain, and upgrade your office to keep your business running smooth.
Phone: 630-953-3100
Email: Contact@tomorrowssolutions.com