Network Security Insights
How to Prevent Ransomware at Work
Learn how to prevent ransomware with practical steps for backups, email security, access control, patching, and employee training.
Struggling to Read Tiny Text During Work or Presentations?
Squinting at your screen? Struggling to read tiny text during work or presentations? Here's a Windows shortcut that can save you time." Instead of adjusting your display settings or moving closer to the screen, Windows already has a built-in solution. Simply press the...
How to Secure VPN Access for Your Business
Learn how to secure VPN access for your business with stronger authentication, tighter policies, and safer remote connectivity.
Office 365 Migration Checklist for SMBs
Use this Office 365 migration checklist to plan email, files, security, and user setup with less downtime and fewer post-migration issues.
Managed Network Monitoring Checklist
Use this managed network monitoring checklist to reduce downtime, improve security, and keep your business network visible, stable, and protected.
Cyber Insurance IT Requirements Explained
Cyber insurance IT requirements are getting stricter. Learn what insurers look for, where companies fall short, and how to prepare.
Best Firewall for Offices: What to Choose
Looking for the best firewall for offices? Learn what matters most, which features to prioritize, and how to choose the right fit.
Business Backup Retention Policy Basics
A business backup retention policy helps protect data, reduce risk, and meet compliance needs. Learn what to keep, for how long, and why.
Stay Protected Before Problems Start
When was the last time you tested whether your backups could actually be restored, reviewed who still has access to your systems, or checked that every device was fully updated? These are the kinds of things that gradually slip down the priority list over time....
Windows Server Support Checklist for SMBs
Use this Windows server support checklist to reduce downtime, tighten security, document systems, and keep your business operations running.
Phishing Prevention for Employees That Works
Phishing prevention for employees starts with clear training, safer systems, and fast reporting. Learn what actually reduces business email risk.
Teams Update Helps Prevent Accidental Meeting Exits
Ever accidentally left a Microsoft Teams meeting? You meant to click another button, maybe Share to present your screen, and suddenly you’re back on your desktop while the meeting carries on without you. Definitely not the smoothest moment. For years, this has been a...
WISP Compliance for Small Business
WISP compliance for small business starts with clear policies, real safeguards, and practical IT controls that reduce risk and support audits.
Meraki Support for Business Networks That Lasts
Meraki support for business networks helps reduce downtime, improve security, and keep Wi-Fi, firewalls, and switching stable.
Why Copilot Isn’t Replacing Your Most Essential Windows Tools
If you work on Windows every day, here’s something worth thinking about: What’s the one app you rely on the most? According to Microsoft’s latest messaging, the answer should be Microsoft Copilot. The company is positioning Copilot as the top productivity app in...
Remote IT Support for Offices That Need Uptime
Remote IT support for offices helps reduce downtime, improve security, and keep staff productive with fast issue resolution and expert oversight.
SonicWall Firewall Management Services Explained
SonicWall firewall management services help businesses reduce risk, improve uptime, strengthen VPN security, and stay ahead of threats daily.
Why AI Shouldn’t Handle Your Password Security
Artificial intelligence is changing the way businesses work. It can write emails, analyze data, automate tasks, and even help detect cyber threats faster than humans. But there’s one security essential you should never hand over completely to AI: Decision-making about...
Onsite Versus Remote IT Support Explained
Compare onsite versus remote IT support for security, speed, cost, and uptime so your business can choose the right mix for daily IT needs.
10 Small Business Cybersecurity Questions
Get clear answers to small business cybersecurity questions, from ransomware and MFA to backups, remote access, compliance, and risk.
7 Best Business Internet Failover Options
Compare the best business internet failover options for uptime, security, and cost so your office stays connected during ISP outages and service cuts.
7 Hybrid Work Security Trends to Watch
Hybrid work security trends are changing fast. Learn what SMBs should watch now to reduce ransomware risk, secure access, and support compliance.
How to Prepare a WISP for Your Business
Learn how to prepare WISP documents for your business with practical steps to assess risk, define safeguards, assign roles, and stay compliant.
Penetration Testing Report Example for SMBs
See a penetration testing report example for small businesses, including key sections, findings, risk ratings, and what to do after the test.
7 Best Disaster Recovery Strategies
Learn the best disaster recovery strategies to reduce downtime, protect data, and keep your business operating after outages, attacks, or failures.
Office 365 vs Google Workspace
Office 365 vs Google Workspace: compare security, email, file sharing, compliance, and cost to choose the right fit for your business.
How to Set Up Business VoIP Right
Learn how to set up business VoIP with the right internet, phones, security, and call flow so your team gets reliable service and fewer issues.
Small Business Penetration Testing Basics
Small business penetration testing helps find real security gaps before attackers do. Learn what it covers, costs, and when to schedule it.
How Often Replace Firewalls? A Realistic Timeline
How often replace firewalls? Most businesses should review them yearly and plan replacement every 5-7 years or sooner for risk and compliance.
How to Configure Office 365 Security
Learn how to configure Office 365 security for small businesses with practical steps to reduce risk, protect email, files, and user access.
How to Build Incident Response Workflow
Learn how to build incident response workflow steps that reduce downtime, contain threats fast, and protect your business operations.
What Would Happen If Your Business Suddenly Lost Access to Its Data?
It’s not something most businesses think about every day. Your team logs in, systems are running, files are accessible, and work gets done. Everything feels stable… until something unexpected happens. A cyber attack. A hardware failure. An accidental deletion. Even a...
Business Continuity Planning Guide for SMBs
A business continuity planning guide for small and midsize businesses to reduce downtime, protect data, define roles, and recover faster.
Why Are Some Businesses Always Dealing with IT Problems?
Some businesses spend a lot of time reacting to IT problems. A computer slows down. A system crashes. Emails stop syncing. Someone reports the issue, waits for support, and work eventually continues—until the next problem shows up. Over time, that cycle becomes...
VoIP Versus Traditional Phone Systems
Compare VoIP versus traditional phone systems for cost, security, reliability, and growth so your business can choose the right fit.
Are You Confident in Your IT Setup?
Confidence in your business technology isn’t just about having the right tools—it’s about understanding what’s going on behind the scenes. If you paused for a moment, could you confidently answer a few key questions? For example: Are your backups running regularly and...
9 Managed IT Services Benefits for SMBs
Learn the top managed IT services benefits for small and midsize businesses, from tighter security and less downtime to predictable support costs.
Stay Focused with Windows 11
Too many pop-ups breaking your concentration? 😤 Here’s a quick Windows 11 feature that fixes that. Click the Start menu…Go to Settings…Select System… then Focus.Set how long you want to stay distraction-free…Then hit Start Focus Session. Just like that—notifications...
What Causes Office Network Downtime?
Learn what causes office network downtime, from hardware failures to security gaps, and how small businesses can reduce outages and risk.
How to Pass Security Audit Without Scrambling
Learn how to pass security audit reviews with better documentation, access controls, backups, and vendor oversight before gaps become findings.
Why Business WiFi Keeps Dropping
Why business wifi keeps dropping often comes down to interference, poor design, aging gear, or security settings. Here’s how to fix it fast.
Ransomware Recovery Plan Checklist
Use this ransomware recovery plan checklist to reduce downtime, protect data, and restore operations with clear, practical recovery steps.
This Windows 11 Feature Will Save You Time Every Day
Always hunting for the same files? 👀Yeah… that gets old fast. Digging through folders again and again?There’s a quicker way. In Windows 11, you can pin files as Favoritesand keep them just one click away. Open File ExplorerFind your fileRight-click itThen hit “Add to...
Network Segmentation for Compliance
Network segmentation for compliance helps reduce risk, limit lateral movement, and support audits with clearer controls, access rules, and scope.
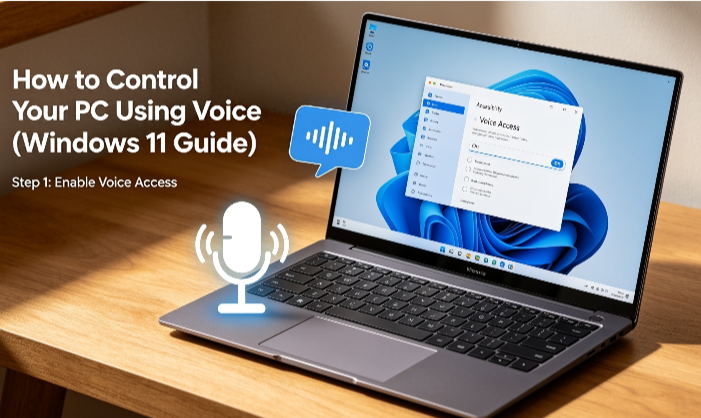
How to Control Your PC Using Voice (Windows 11 Guide)
Still clicking everything on your computer? Watch this… You can control your entire PC… using just your voice.Turn on Voice Access in Windows 11 under Accessibility settings.Open apps, scroll pages, click buttons, and even type emails… hands-free.Perfect when you're...
Cybersecurity Risk Assessment Guide for SMBs
A cybersecurity risk assessment guide for SMBs to identify threats, rank risks, close gaps, and support compliance without slowing operations.
Windows 10 Is Running Out of Time—Are You Ready?
Windows 10 may still feel “fine” under Extended Security Updates (ESU), but that sense of security is temporary. Standard support already ended in October 2025, and ESU will expire in October 2026—after which there will be no more security updates or protection. Many...
SMB Cyber Insurance Trends in 2026
SMB cyber insurance trends are changing fast. Learn what insurers now require, what drives premiums, and how small businesses can stay insurable.
Why Most AI Projects Stall And How to Fix It
A lot of AI projects don’t fail because the tech doesn’t work—they stall because businesses lack clarity and confidence. Many companies jump into AI without a specific problem to solve, so projects stay stuck in testing mode with no clear success metrics. On top of...
Free Cybersecurity Assessment for Business
Get a free cybersecurity assessment for business to find risks, close gaps, and improve ransomware protection, compliance, and uptime fast.
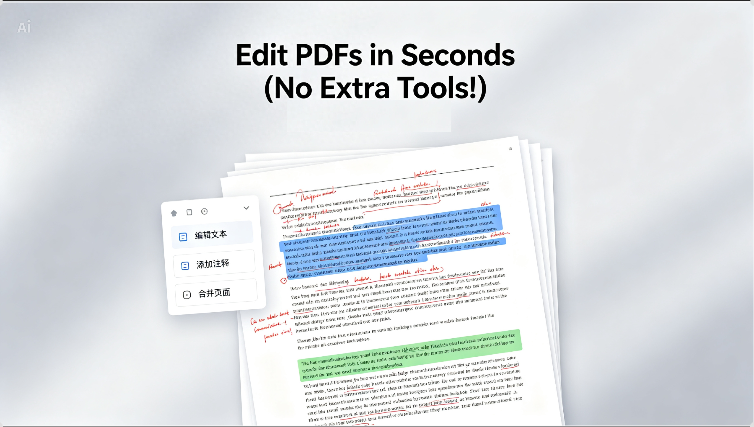
Edit PDFs in Seconds (No Extra Tools!)
Ever been sent a PDF… and needed to change something fast?But it won’t let you edit it?Here’s a quick trick most people don’t know…Just open the PDF in Microsoft Word… it’ll convert it automatically.Now you can edit the text like a normal document.And save it back as...
Network Documentation and Password Management
Network documentation and password management reduce downtime, improve security, and help businesses stay ready for audits and staff changes.
Server and Desktop Support Services That Work
Server and desktop support services help Chicago-area businesses reduce downtime, improve security, and keep staff productive every day.
Disaster Recovery Planning for SMB
Disaster recovery planning for SMB helps reduce downtime, protect data, and keep operations moving after cyberattacks, outages, or hardware failure.
Choosing Business Data Backup Solutions
Choosing business data backup solutions means balancing recovery speed, security, compliance, and cost before ransomware or outages hit.
Make Your Windows 11 PCs Last Longer
Many businesses replace computers too early—not because they’re broken, but because they’ve slowed down over time. In most cases, that slowdown isn’t hardware failure. It’s small, fixable issues building up. A few simple habits can significantly extend the life of...
Office 365 Support for Small Business
Office 365 support for small business helps reduce downtime, improve security, manage users, and keep email, files, and Teams running well.
Tired of Switching Tabs? Do This Instead
Still flipping back and forth between tabs like this? It’s slow… and honestly, kind of annoying. Here’s a simple Chrome trick you might not know… Just drag one tab to the side… then snap both windows side by side. Now you can see both pages at once—no more switching....
Ransomware Protection for Small Business
Ransomware protection for small business starts with backups, MFA, training, and fast response planning to reduce downtime and data loss.
Penetration Testing for Small Business
Penetration testing for small business helps uncover security gaps before attackers do. Learn what it covers, when to do it, and what to expect.
Secure VPN Setup for Small Business
Learn how a secure vpn setup for small business protects remote access, supports compliance, and reduces risk without slowing daily work.
OneNote Getting Messy
OneNote getting messy? Everything’s there… but nothing’s easy to find. Try this simple trick 👇. Highlight key points (just like this). Add tags to what matters. Then use ‘Find Tags’ to pull everything up instantly. Now your notes actually work for you ✨”...
Business Firewall Support Services That Work
Business firewall support services help protect data, secure remote access, reduce downtime, and keep small businesses compliant and operational.
Network Cabling and Fiber Optic Installation Service
Need network cabling and fiber optic installation service? Build faster, safer, more reliable business networks with proper design and clean installs.
9 Managed IT Services Examples for SMBs
See 9 managed IT services examples that help small businesses reduce downtime, strengthen security, support staff, and plan IT costs.
Managed IT Services for Small Businesses Near Me
Looking for managed IT services for small businesses near me? Learn what local support should include, what to ask, and how to choose wisely.
Don’t forget to protect your browsing privacy.
When you open a browser on your phone, what does it actually know about you?More than most people realize.A recent analysis of popular mobile browsers found that apps like Chrome and Edge collect a wide range of data — not just your browsing history, but also things...
AI Phishing Is Here. Are You Ready?
Phishing scams used to be easy to spot because they were mass-produced and often poorly made. But that’s changing. With the rise of AI, scammers can now create more advanced, personalized phishing attacks that are generated in real time for each victim. Instead of one...
What Is Managed IT Services for SMBs?
What is managed IT services? Learn how it helps small businesses reduce downtime, improve security, control costs, and support daily operations.
What Is a Managed Service Company?
What is a managed service company? Learn how it supports security, uptime, compliance, and daily IT for small and midsize businesses.
It’s time to govern your team’s AI use.
AI tools like ChatGPT and Gemini are now widely used in the workplace, helping teams boost productivity through faster writing, analysis, and problem-solving. But this rapid adoption has outpaced governance. Many employees are using AI through personal or unsanctioned...
Why MFA stops old password attacks?
An old password attack usually means: Someone got your password from a past data breach Or they’re trying previously used passwords (“password reuse”) Without protection, that can still work if you haven’t changed it everywhere. MFA stops old password attacks because:...
5 New Trends from a Study on the State of AI at Work
Technological progress is advancing at an unprecedented rate, and it's no surprise to anyone who's witnessed the ChatGPT phenomenon. AI trends are reshaping industries, with artificial intelligence (AI) standing at the heart of this transformation. Businesses are...
Guide to Smart Windows 11 Settings to Boost Your Productivity
The latest Windows operating system, Windows 11, is quickly catching up to its predecessor, Windows 10. By August 2024, Windows 11 claimed over 31% of the Windows market share, and this number is expected to rise sharply as Windows 10 is set to retire in 2025. Have...
Protect Yourself: 8 Steps to Take When You Get a Notice Your Data Was Breached
When a data breach occurs, it leaves you feeling vulnerable. You might receive an email or letter from a company notifying you that your data has been compromised—a scenario that's all too common nowadays. Data breaches can happen at banks, social media platforms like...
Watch Out for Google Searches – “Malvertising” Is on the Rise!
Malware comes in various forms, and one of the most prevalent is known as “malvertising.” It appears across multiple platforms, from social media networks to websites. These harmful ads can even be found in Google search results. Malvertising has become increasingly...
Cyber Experts Say You Should Use These Best Practices for Event Logging
In today’s evolving digital world, businesses face a growing array of cybersecurity threats. From sophisticated phishing schemes to ransomware attacks, the dangers are becoming more complex and pervasive. How can you protect your organization in this environment?...
7 Great Examples of How AI is Helping Small Businesses
Artificial Intelligence is no longer exclusive to large corporations with deep pockets. Today, small businesses can leverage AI tools to streamline operations, enhance customer experiences, and drive profitability, making it an accessible solution for growth and...
Top Technologies Transforming Customer Service Today
Customer service is the cornerstone of any thriving business. As customer expectations constantly shift, companies must adapt their strategies and tools to stay aligned with these changes. 55% of customers like self-serve customer service over speaking to a...
Data Breach Damage Control: Avoid These Pitfalls
Data breaches are an unavoidable risk for businesses, regardless of their size. When a breach happens, swift and strategic action is essential. How a company handles the aftermath can have lasting effects on its reputation, financial health, and legal standing. The...
Copilot in Teams – New Features, Agents & More
Microsoft Teams is constantly advancing, establishing itself as a central platform for collaboration and communication in today’s workplace. Adding AI-powered Copilot takes Teams to new heights, transforming how we engage with technology to optimize workflows, boost...
Navigating the Challenges of Data Lifecycle Management
Data stands as one of the most prized assets for any business. Overseeing its journey from creation to disposal can be complex. Data lifecycle management (DLM) encompasses a series of strategies and protocols that dictate how data is handled, stored, and ultimately...
6 Simple Steps to Enhance Your Email Security
Email remains an essential communication tool for both businesses and individuals. However, it’s also a primary focus for cybercriminals. With cyberattacks growing more advanced, strengthening your email security is more crucial than ever. A staggering 95% of IT...
8 Strategies for Tackling “Technical Debt” at Your Company
Remember when your company’s software flowed like a well-oiled machine, effortlessly achieving results? Now, does it feel like navigating a maze of workarounds, emergency fixes, and half-baked solutions? Enter the realm of technical debt. This hidden, gradual buildup...
Enhancing Employee Performance with a Mobile-Optimized Workspace
In today’s fast-paced business environment, adaptability is key. Workspaces are no longer confined to physical offices. Employees now collaborate effortlessly from any location, whether it’s at a local café or from the comfort of their own homes. This is the power of...
Essential Settings to Maximize Your Microsoft 365 Experience
Microsoft 365 offers an impressive array of tools designed to boost productivity and collaboration, particularly for small to mid-sized businesses (SMBs). However, many businesses only tap into a fraction of its capabilities. To fully unlock its potential, optimizing...
Why Securing Your Software Supply Chain is Critical
In today’s interconnected world, every part of your business relies on software, whether it’s hosted locally or in the cloud. Securing the entire lifecycle of your software supply chain—starting from the tools developers use to the delivery of updates—is crucial. A...
Don’t Be a Victim: Common Mobile Malware Traps
Your smartphone is more than just a communication tool; it's a digital wallet, personal assistant, and storage hub for sensitive information. From banking details to private photos, it holds a wealth of data, making it a prime target for cybercriminals. While many...
6 Helpful Tips to Troubleshoot Common Business Network Issues
A business network is the foundation that supports all your digital operations. It's the invisible force that connects everything from emails to mission-critical apps and cloud services. When that connection is interrupted, the results can be severe. Communication...
What Things Should You Consider Before Buying a Used Laptop?
Purchasing used laptop can offer significant savings, but it also comes with potential risks. A careful and thorough evaluation is essential to avoid wasting your money. When buying used tech, it’s crucial to look beyond just the exterior. This guide will walk you...
Onsite And Remote Services To These Cities
Contact Tomorrow’s Internet Solutions Today
Thank You for visiting our site. We are available for remote and onsite service. On most days, we are available by phone starting at 6:30 AM for remote support or a free consultation.
With over sixty years of in-house IT experience, our team can install, maintain, and upgrade your office to keep your business running smooth.
Phone: 630-953-3100
Email: Contact@tomorrowssolutions.com